Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
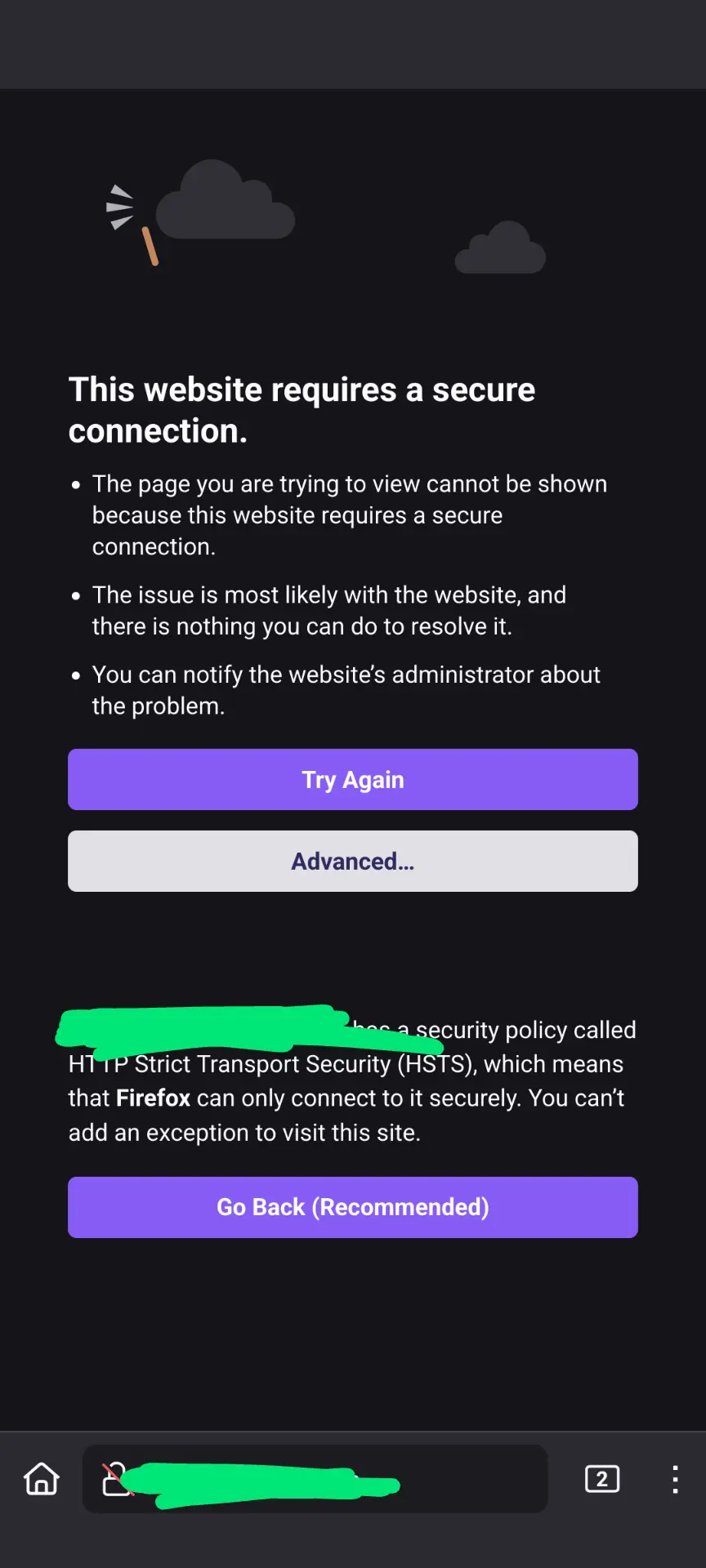
You're getting a bad TLS certificate. If you press the Advanced button you should be able to see a reason why the certificate is not accepted by the browser.
It can be any reason, for example I got this error when one of my certificates expired (because I messed around with the DNS API token's permissions and didn't test it afterwards).
In your case it's probably not an expired certificate because then you'd see that error everywhere not just on the hospital WiFi.
I suspect that whoever controls that WiFi is trying to hijack your connection, but it won't work because once a browser has seen a HSTS flag it will refuse to connect to that site in any way except TLS (with the correct certificate ofc).
Kudos for enabling HSTS btw, excellent move.
I'll be very curious to see what the browser says the reason is.
And yes the HSTS error is completely unhelpful in this scenario. The fact HSTS blocks the connection is secondary, the much more important detail is why TLS could not be established.
It's like if your house key didn't work and you were told "you know, doors require a key to be unlocked". You'd be like "dude, I know, I have the key right here, why isn't it working?"
I don't plan on being back at the hospital for a while, so I guess we'll never find out!
I use a wildcard certificate, I wonder how common that is? That might be something they block, but yeah... I wonder why.
FWIW when you can't connect to a website Firefox shows you the "hm we're having trouble finding that site" error.
Nah, wildcard cert wouldn’t play into it at all.