Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
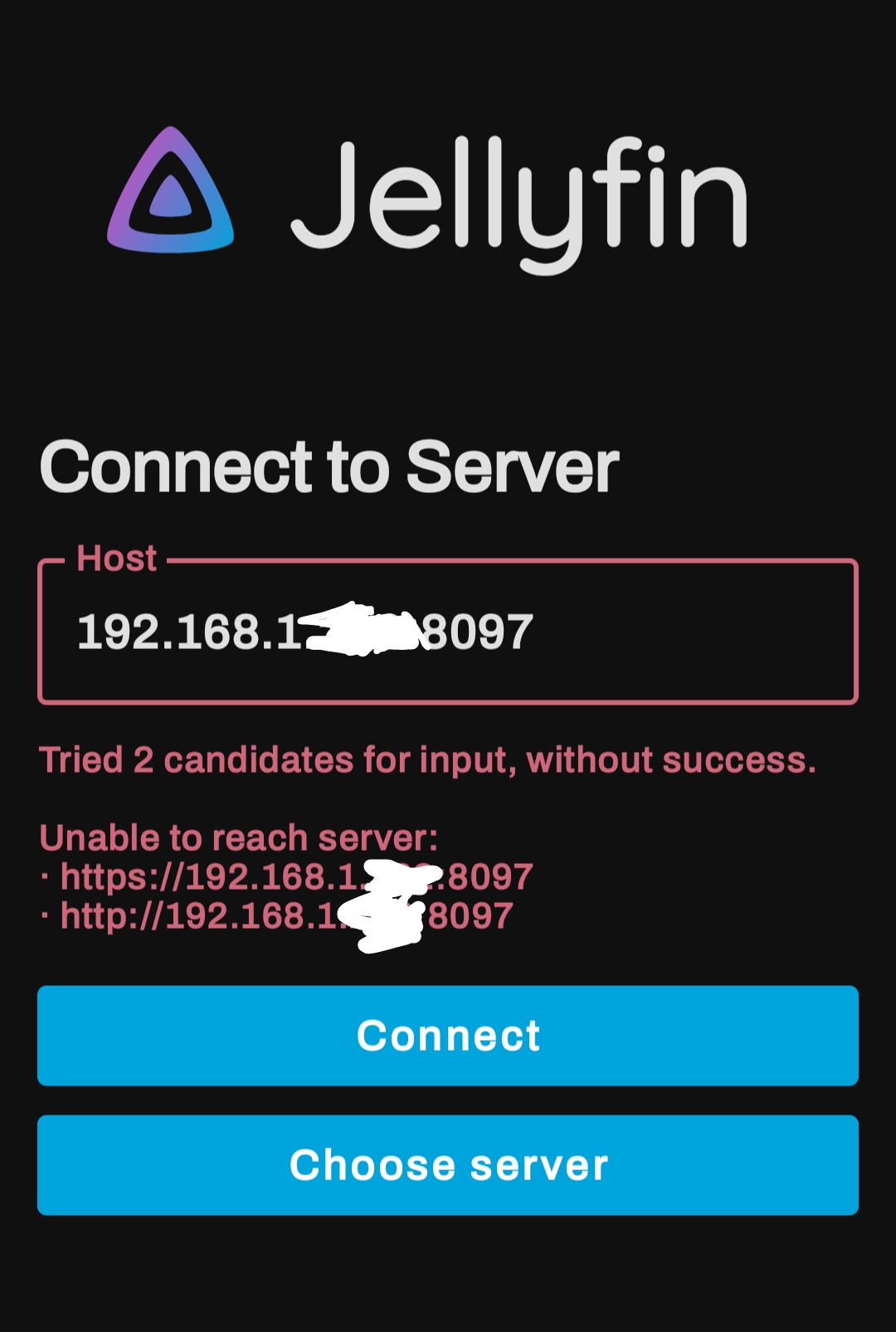
You don't need to put in the effort to hide those IPs. An IP starting with 192.168 is a private network and virtually useless as any way to compromise your network - an outsider would need access to your network (via your modems public facing IP) and know the device access credentials to make any use of the IPs.
That being said, it appears your input devices are unable to connect because they can't be found. That means a mismatch in network details somewhere. Check the IP address and confirm it's using the same subject; does the device connecting use the same 192.168.1.x network as the input/source device?
No I have his ip and now I will hax!!!